JAKARTA - North Korean-affiliated hackers are reportedly using macOS-specific advanced malware to target Web3 and crypto companies. The malware is spread through fake Zoom invitations, with the aim of stealing sensitive data and avoiding detection of standard security systems.
A report from SentinelOne Labs reveals that this attack uses a layered method, which involves social engineering techniques, malicious AppleScript, and a compiled binary file using Nim's programming language language that is rarely used in macOS making it difficult to detect.
This cyber campaign, named 'NimDoor', shows the new tactics North Korean hacker groups use to penetrate the security system and steal data from companies engaged in the crypto sector.
How The Attack Takes Place
Attacks usually start with social engineering. The attacker disguised himself as a trusted contact via the Telegram app, then invited the victim to schedule Zoom calls via the Calendar link.
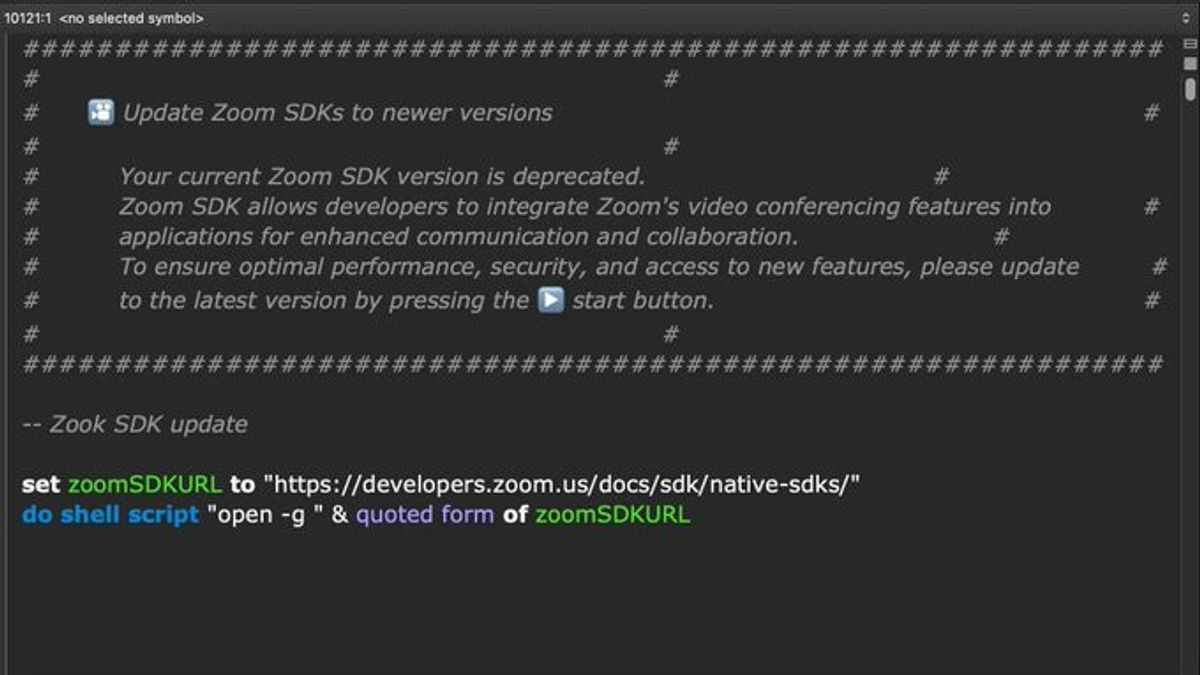
The victim received a phishing email containing a fake Zoom SDK update file, in the form of a malicious AppleScript that has thousands of "paddings" rows to avoid detection. This script then downloads additional malware from hacker-owned servers that mimic official Zoom domains.
Two main binary files were discovered by researchers one written in C++ and another in Nim used to create fixed access and steal data.
Advanced Techniques For Access And Data Theft
This malware uses unusual methods in macOS such as process injection with special access rights, encrypted communication via WebSocket TLS (wss), as well as signal-based persistence mechanisms.
This malware will be installed again if the user tries to turn it off or when the system is rebooted. To steal data, this malware uses Bash scripts that extract browser history, credentials from Keychain, and Telegram data.
The targeted browser includes Arc, Brave, Firefox, Chrome, and Microsoft Edge. In fact, this malware retrieves an encrypted local Telegram database for offline possibilities.
Licik Persistence Technique
To stay in the system, malware takes advantage of macOS Launchagents with names that resemble original files, such as Googlee LLC (switching small L letters with i large), to look like files from Google. There is also a file called CoreKitAgent that monitors the system's signal and reinstalls itself if it is stopped.
This malware is equipped with an anti-analytic feature, such as an asynchronous break of 10 minutes to avoid detection in the sandbox.
SEE ALSO:
Evolution Of Attack Equipment
According to SentinelOne, Nim's language use shows improved tool capabilities used by hackers. Nim's ability to run codes during compilation and incorporation of developer codes with runtime codes makes static analysis difficult.
AppleScript-based banners allow light long-range controls without the need to use heavy exploit frameworks that are more easily detected by security systems.
How To Protect Yourself From NimDoor
1. Do not run the script or software update received via suspicious email or message, even though it looks like it comes from a trusted contact.
2. Check the URL carefully because hackers often use mock domains.
3. Always update macOS systems and apps to the latest version to close security loopholes.
4. Use a trusted endpoint security app that can detect process injections, malicious AppleScripts, or suspicious launcher agents.
5. Check login items and Launchagents regularly to detect invalid entries.
6. Use strong and unique passwords, as well as enable two-factor authentication (2FA) wherever available.
The English, Chinese, Japanese, Arabic, and French versions are automatically generated by the AI. So there may still be inaccuracies in translating, please always see Indonesian as our main language. (system supported by DigitalSiber.id)